In an increasingly technological world, personal data runs the risk of being exposed — but researchers are on their way to tightening data security requirements.
While most of the roughly 30,000 daily hacking attempts that could happen at a large research university like UNC bounce off firewalls, even a small breach can threaten the entire system.
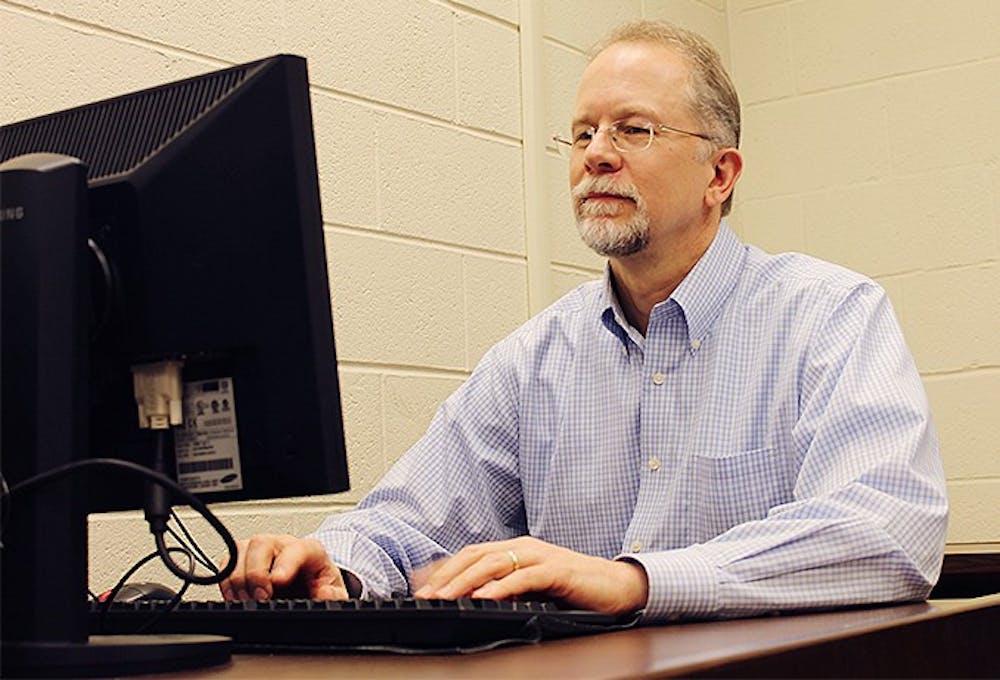
“If one little bit of spyware finds a crevice and crawls in and sits there, you have a potential breach,” said Dan Nelson, professor and director of the Office of Human Research Ethics at UNC.
As society moves into an entirely digital environment, Nelson said researchers have had to change their methods of securing data. Data security doesn’t mean spreadsheets locked in a filing cabinet anymore — everything is online.
“(Technological advances) increase the power of the science, but it also increases our exposure to potential breaches of confidentiality, either intentional or accidental,” he said.
And now, there is a big push for universities and their respective Information Technology Services to work together to help researchers secure their data — especially sensitive personal data, including medical records, sexual behavior, illegal substance abuse or immigration status.
“Most researchers may be trained to collect and analyze data but aren’t necessarily trained to know how many bits of encryption are needed to meet current security standards,” Nelson said.
He said the Office of Human Research Ethics, which is responsible for ethical and regulatory oversight of any research at UNC involving humans as subjects, receives more than 4,000 research projects annually that must go through a review process before being approved.
The office developed a system to assess the level of security that might be needed for a given research project, Nelson said.